Verified Tech Access centers on trusted channels and auditable provenance for business contacts. The approach favors independent validation, current credentials, and clear ownership to reduce risk. Privacy-minded controls aim to minimize exposure while preserving access. Yet, questions remain about governance, cross-functional autonomy, and real-world enforcement. What gaps might undermine reliability, and how can organizations balance speed with prudent oversight? This tension invites careful scrutiny before committing to any verified contact or process.
What Is Verified Tech Access and Why It Matters
Verified Tech Access refers to the ability of a business to obtain and deploy trusted technical resources, tools, and services with guaranteed legitimacy and ongoing support.
The concept centers on reducing risk through verified access and vetted pathways. It emphasizes transparency, governance, and sustainability.
Trusted channels enable durable partnerships while preserving autonomy, minimizing vendor lock-in, and supporting informed, freedom-minded decision-making.
How Verification Works for Trusted Business Contacts
The process of verifying trusted business contacts builds on the prior discussion of verified tech access by outlining concrete checks, controls, and assurances that distinguish legitimate partnerships from risk-prone arrangements.
Verification workflow operations emphasize due diligence, lineage, and independent validation. A skeptical frame remains essential: trusted contact credentials must be current, auditable, and resistant to manipulation, reducing exposure without stifling entrepreneurial freedom.
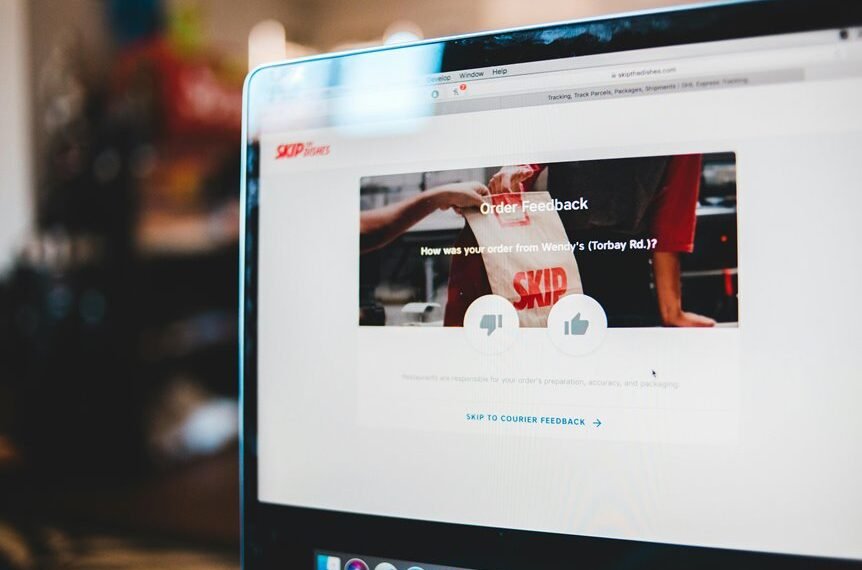
Best Practices to Use Verified Channels Without Risking Privacy
In trusted communications, adopting verified channels requires a disciplined balance between accessibility and privacy safeguards. The guidance remains pragmatic, not permissive: verify identities with privacy conscious verification, minimize data exposure, and avoid broad sharing.
Employ secure contact sharing practices, limit distribution, and audit access trails. Skepticism guards against complacency; freedom demands persistent privacy discipline, even when trusted networks claim convenience.
Real-World Scenarios: Boosting Collaboration With Verified Access
Real-world collaboration benefits from concrete, verifiable access controls that prevent data spill while enabling efficient teamwork. In practice, verified access accelerates cross-functional projects but demands disciplined use of a collaboration protocol and clear ownership. Skeptics note potential bottlenecks; proponents argue for streamlined access governance that preserves autonomy while reducing risk, enabling freedom without unnecessary surveillance or overreach.
Conclusion
In a world of shifting signals, verified tech access stands as a fixed beacon. A lighthouse on a foggy shore, its light traces trusted routes through corridors of permission and audit trails. Yet the harbor is only as secure as its guards: ongoing validation, transparent lineage, and disciplined privacy. For skeptics, the promise remains provisional—visible, tangible in practice but fragile without consistent governance, durable partnerships, and vigilant, auditable oversight. The voyage depends on verifiable, enduring footing.